Quantum-Safe Push, AI-Secure Browsing, And Major Threat Disruptions
Coverage: 28 Jan 2026 (UTC)
< view all daily briefs >Post‑quantum readiness and AI‑safe productivity took center stage as CSO detailed a new crypto‑visibility and remediation platform from Palo Alto Networks, and Google Cloud outlined enterprise browser controls pairing agentic AI with granular data protections. Alongside these prevention‑first moves, fresh advisories landed across widely used software, and defenders coordinated a disruption of a large residential proxy network that had been abused at scale.
Platform defenses move first
Palo Alto Networks introduced Quantum‑Safe Security as a central intelligence layer that continuously discovers cryptographic use across networks, applications, infrastructure and IoT, analyzes protocol and cipher choices, and correlates encryption strength with business criticality to prioritize remediation. The roadmap stages modernization toward “quantum‑ready” posture, activation of post‑quantum or hybrid algorithms where feasible, and real‑time encryption translation for legacy assets that cannot be upgraded. Governance features include a living cryptographic inventory (CBOM), real‑time weak‑cipher detection, and audit/reporting aligned with standards such as NIST, FIPS 140‑3 and DORA. The platform integrates with SIEM, EDR, load balancers and vulnerability tooling to support scalable deployment and crypto hygiene at enterprise scale; the vendor also emphasized the harvest‑now, decrypt‑later risk behind proactive transition planning.
On the endpoint, Chrome Enterprise set a course for the browser as a managed, agentic workspace powered by Gemini 3 models across operating systems. The vision couples automation with controls: enhanced DLP (real‑time copy/paste rules, masking for content typed to LLMs, dynamic watermarking), admin switches to enable or block AI features by group, and restrictions on unapproved external generative AI services. Google described a double‑check review mechanism for agent actions and strict scoping so agents can only access the specific sites needed for a task, plus operational guardrails like extra evaluation time for major AI features and coordination with Workspace to extend protections.
AWS expanded resiliency testing by integrating DynamoDB multi‑Region strong consistency (MRSC) global tables with Fault Injection Service, letting teams pause replication to one or more regions and observe failover logic, monitoring and client behavior under controlled regional‑failure scenarios. The capability targets high‑availability workloads and business continuity drills across supported regions.
Google Cloud positioned Spanner as an intelligent context hub for AI with expanded multi‑model support (vectors, graphs, full‑text), integrations with Vertex AI, and operational features including an index advisor, schema recommendations, and a new CLI. Safety additions such as drop protection and default backup schedules aim to reduce human error, while performance and cost optimizations target lower latency and TCO for global deployments.
Advisories and patches
A critical sandbox escape in the popular Node.js library vm2 (CVE‑2026‑22709) allows arbitrary code execution via Promise callback sanitization gaps; upgrading to 3.10.2 or later is advised, and organizations are reminded that airtight in‑process sandboxing in JavaScript remains difficult. Details and guidance are outlined by CSO.
Two vulnerabilities in the n8n automation platform enable full remote code execution under certain conditions: CVE‑2026‑1470 (JavaScript AST escape via the legacy with statement) and CVE‑2026‑0863 (Python AST escape). Fixes are available in specified 1.x and 2.x releases; administrators should update immediately, review who can create or modify workflows, and rotate exposed secrets, per Infosecurity.
BleepingComputer reports that SolarWinds Web Help Desk updates remediate multiple critical issues, including unauthenticated remote command execution (deserialization) and authentication bypasses, with an additional hardcoded credentials flaw. Customers are urged to move to Web Help Desk 2026.1 and review administrative credentials.
Google’s threat team highlighted widespread active exploitation of WinRAR CVE‑2025‑8088, a path‑traversal bug used by multiple state‑aligned and financially motivated actors to achieve persistence via the Startup folder. Upgrading to WinRAR 7.13 or later and monitoring for suspicious archive extraction behaviors are recommended, per The Hacker News.
Infosecurity covered AISLE’s coordinated disclosure of 12 OpenSSL flaws across multiple subsystems, including a high‑severity stack overflow in CMS parsing. Maintainers incorporated fixes into January 2026 updates; users should apply the releases to reduce crash and potential RCE risk.
Takedowns and supply chain
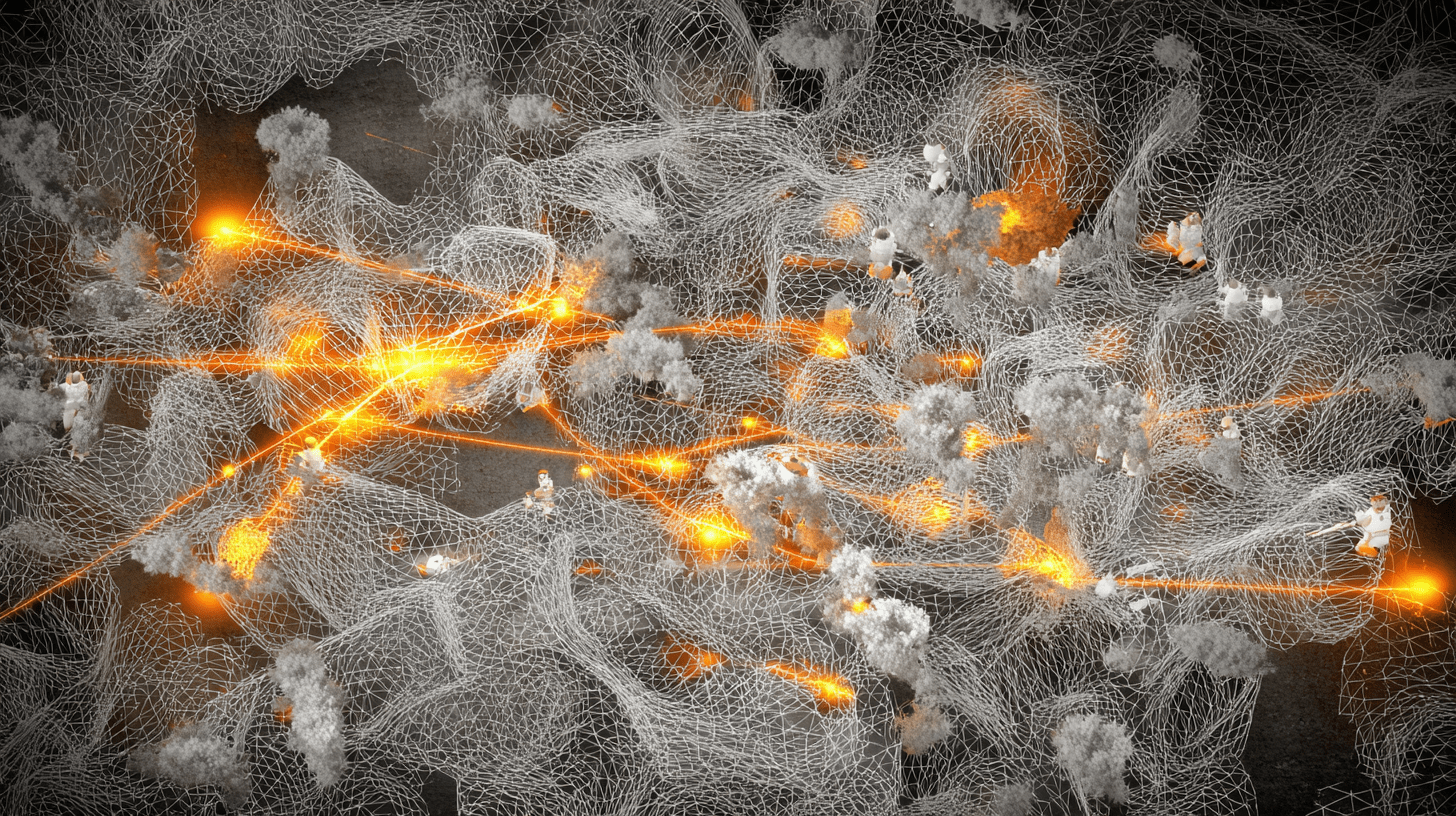
Google Cloud described a multi‑pronged operation against IPIDEA, a large residential proxy network built from monetization SDKs and trojanized binaries. The effort combined court‑ordered domain takedowns, intelligence sharing on SDKs and a two‑tier C2 model, and Google Play Protect enforcement, disrupting roughly 7,400 Tier Two servers and reducing the pool of enrolled consumer devices. GTIG observed more than 550 tracked threat groups using the exit nodes in a single week, spanning botnets, espionage and access campaigns. Separately, BleepingComputer reports eScan confirmed an update infrastructure breach that briefly pushed a malicious file via a regional server; the vendor isolated and rebuilt systems, rotated credentials, and issued a remediation update.
Critical infrastructure and exposure risks
BleepingComputer relays findings that a late‑December campaign in Poland impacted around 30 distributed energy sites, disabling communications and remote monitoring at many locations and corrupting configurations on some OT/ICS devices. While power outages did not occur, loss of visibility and control at CHP, wind and solar installations underscores the operational risk in decentralized energy systems.
CISA issued guidance on ongoing exploitation of Fortinet CVE‑2026‑24858, an authentication bypass in FortiCloud SSO affecting FortiOS, FortiManager, FortiWeb, FortiProxy and FortiAnalyzer. Fortinet temporarily disabled SSO service and reinstated it with changes to block exploitation; operators should apply patches, inspect for unauthorized accounts and VPN changes, and follow Fortinet’s mitigations. In parallel, FortiGuard documented EncystPHP, a weaponized PHP web shell deployed via a FreePBX Endpoint Manager flaw (CVE‑2025‑64328), with extensive persistence, credential harvesting and telephony abuse capabilities; patches, IOC hunts and account audits are advised.
CSO reported a publicly accessible database containing approximately 149 million harvested logins, including usernames, plaintext passwords and login URLs across consumer and financial services. The dataset, linked to keyloggers and infostealers, materially lowers barriers for credential‑stuffing and phishing. Users should change passwords and enable multi‑factor authentication; providers can enforce resets and monitor for automated abuse.