AI Defenses Advance as Exploited Bugs and Outages Hit Ops
Coverage: 20 Feb 2026 – 22 Feb 2026 (UTC)
< view all daily briefs >Security teams weighed new defensive tooling against active exploitation and service disruptions. Platform updates focused on AI-enabled code review and safer agent access models, while agencies flagged webmail flaws under active attack. Meanwhile, researchers detailed AI-augmented intrusion tradecraft and several high-impact operational incidents across networks and public services.
AI-assisted defenses move into dev workflows
Anthropic introduced Claude Code Security in a limited research preview, applying AI to scan entire codebases, trace data flows, and propose human-reviewed patches, with multi-stage verification to cut false positives and prioritize fixes. The company stresses a human-in-the-loop model and integration into developer workflows to accelerate remediation without automatic changes. Anthropic frames the rollout as a defensive counter to adversaries also leveraging AI for vulnerability discovery. In parallel, Cloudflare unveiled a server-side Model Context Protocol (MCP) implementation of Code Mode that exposes the full Cloudflare API via two tools—search() and execute()—keeping agent token usage near 1,000 tokens while executing agent-authored JavaScript in a sandboxed Dynamic Worker isolate. The design adds OAuth 2.1 downscoping and controlled outbound handlers, with open-sourced SDKs and plans for MCP Server Portals to compose multiple services behind a fixed-token gateway. Cloudflare positions this approach to combine predictable context cost with progressive capability discovery and safer execution.
Exploited vulnerabilities demand rapid mitigation
Researchers documented in-the-wild exploitation of a critical input-validation bug in BeyondTrust Remote Support and Privileged Remote Access appliances (CVE-2026-1731), enabling OS command execution via a WebSocket-exposed wrapper. Observed intrusions deployed web shells, remote access tools, staged data for exfiltration, and leveraged persistence mechanisms; CISA has listed the flaw in its KEV and responders urge immediate patching, credential rotation, interface restriction, and hunts for WebSocket misuse and shell artifacts. The Hacker News notes links to prior sanitization issues and ransomware activity. Separately, CISA added two Roundcube webmail issues—CVE-2025-49113 (deserialization) and CVE-2025-68461 (XSS)—to the Known Exploited Vulnerabilities catalog, directing FCEB agencies to remediate by set due dates and urging all operators to inventory instances, apply vendor updates, and implement compensating controls. CISA underscores the elevated risk to internet-facing mail systems. Why it matters: both cases involve widely exposed services where exploitation can yield code execution or session manipulation.
AI-augmented intrusions test fundamentals
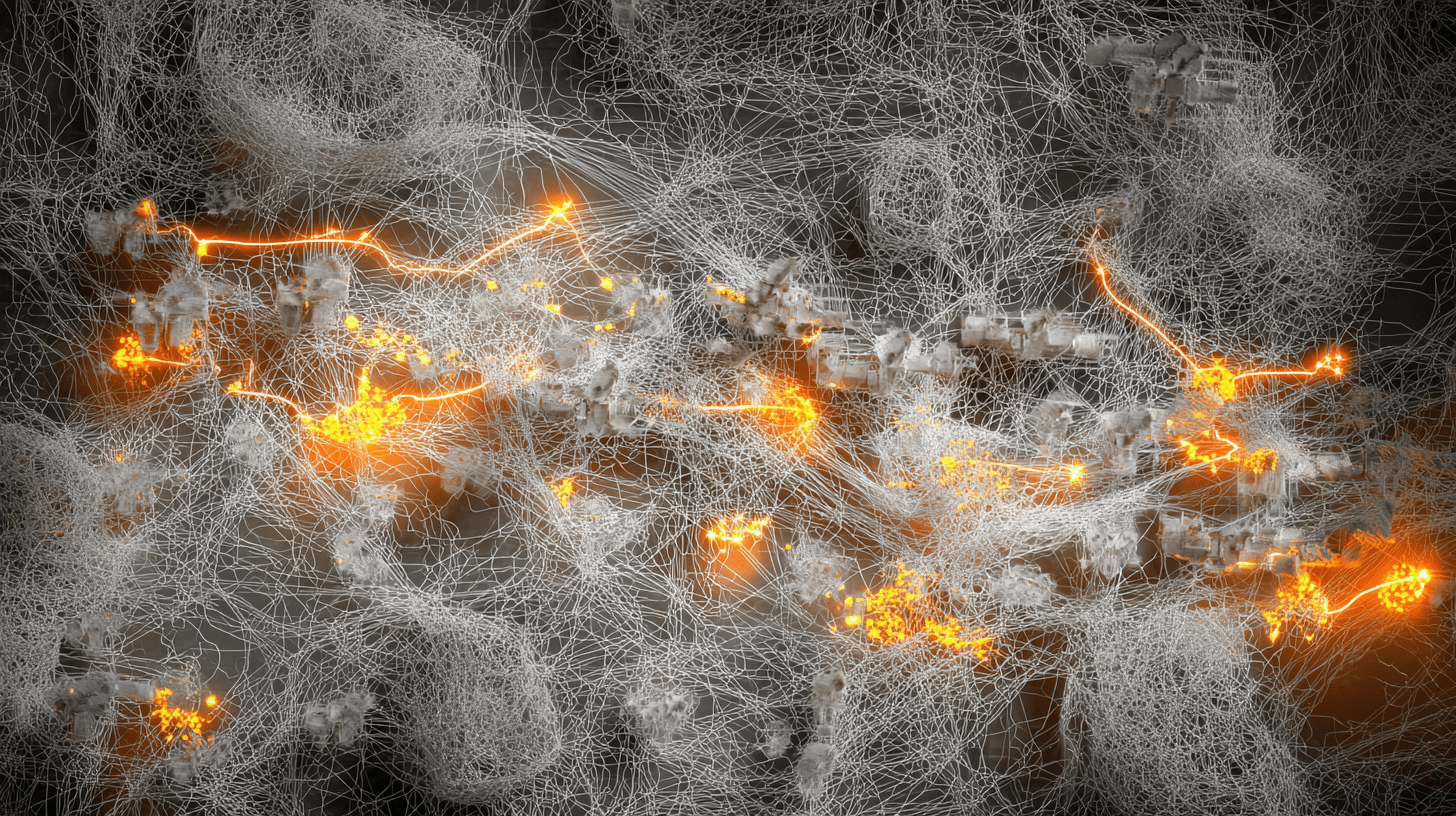
Amazon Threat Intelligence reported a financially motivated actor using multiple commercial generative AI services to compromise more than 600 FortiGate devices across 55 countries by abusing weak, single-factor credentials on internet-exposed management ports. Post-compromise actions included extracting full configurations and credentials, Active Directory DCSync, and attempts to undermine backup recovery by targeting Veeam. Investigators saw AI-assisted tooling used to parse stolen data and plan pivots, with the operator abandoning hardened targets in favor of easier victims. Recommended mitigations: remove public management access, enforce MFA and unique credentials, isolate and harden backup systems, and monitor for DCSync and unauthorized access from VPN pools. AWS shared IOCs and coordinated disruption efforts.
In the software supply chain, researchers detailed a malicious npm publish that altered the popular Cline CLI to silently fetch and execute the agentic AI application OpenClaw via a postinstall script. The tainted release was live for roughly eight hours before maintainers deprecated it and issued a corrected version; guidance urges developers to update Cline and remove OpenClaw if it was not intentionally installed, and to tighten publish workflows and token handling. CSO highlights the risk that agentic tools with broad integrations pose when introduced via developer environments. Why it matters: opportunistic attackers are pairing AI-driven scale with basic hygiene gaps—exposed interfaces, weak credentials, and supply-chain tokens—to achieve impact quickly.
Service disruptions and data exposure
Cloudflare published a postmortem on a February 20 outage traced to a software bug in the system managing Bring Your Own IP addresses. An API change caused an automated cleanup task to misinterpret a parameter and withdraw roughly 1,100 BGP prefixes, impacting a subset of services including 1.1.1.1. Engineers reverted changes and restored most prefixes within hours, with manual updates completing by 23:03 UTC; remediation plans include API schema validation, clearer separation of operational and configured state, rollback snapshots, and improved detection of abnormal withdrawals under the ongoing Code Orange: Fail Small initiative. Cloudflare attributed the incident to a software bug, not malicious activity.
Authorities in France disclosed unauthorized access to the national bank account registry, FICOBA, via credentials stolen from a civil servant, potentially exposing identifiers, account holder data and, in some cases, taxpayer IDs for about 1.2 million accounts; agencies restricted access, notified banks, and warned of increased phishing risk while working to restore operations with enhanced controls. In the U.S., UMMC closed clinics after a ransomware attack disrupted IT systems and access to electronic medical records, while inpatient and emergency care continued under downtime procedures; federal partners and external specialists are assisting the response. BleepingComputer provides details on the FICOBA breach, and BleepingComputer outlines the operational impact at UMMC. Why it matters: registry and healthcare disruptions combine privacy exposure with public service interruption, raising both fraud risks and care delivery challenges.